
Whatsapp, Telegram media files can be manipulated on android devices
A new research by Symantec talks about the dangers of Media File Jacking, a type of attack undertaken by cybercriminals to target media files, which are sent through instant messaging apps like WhatsApp and Telegram, and are stored in external storage of Android phones. The criminals can take advantage of a flaw that exposes these media files and they can then be manipulated by malicious actors, Symantec’s Modern OS Security team has found. The researchers say that this vulnerability stems from the (very short) lapse in time between when media files received through the apps are written to the disk, and when they are loaded in the apps’ chat user interface (UI) for users to consume.
Android apps can store files and data in two storage locations: internal and external storage. Files saved to internal storage are accessible only by the app itself, meaning other apps cannot access them. Files saved to an external storage public directory are world-readable/writeable, so they can be modified by other apps or users beyond the app's control. By default, WhatsApp stores media files received by a device in external storage, and by contrast, in Telegram, this happens only if a user enables the “Save to Gallery” feature.
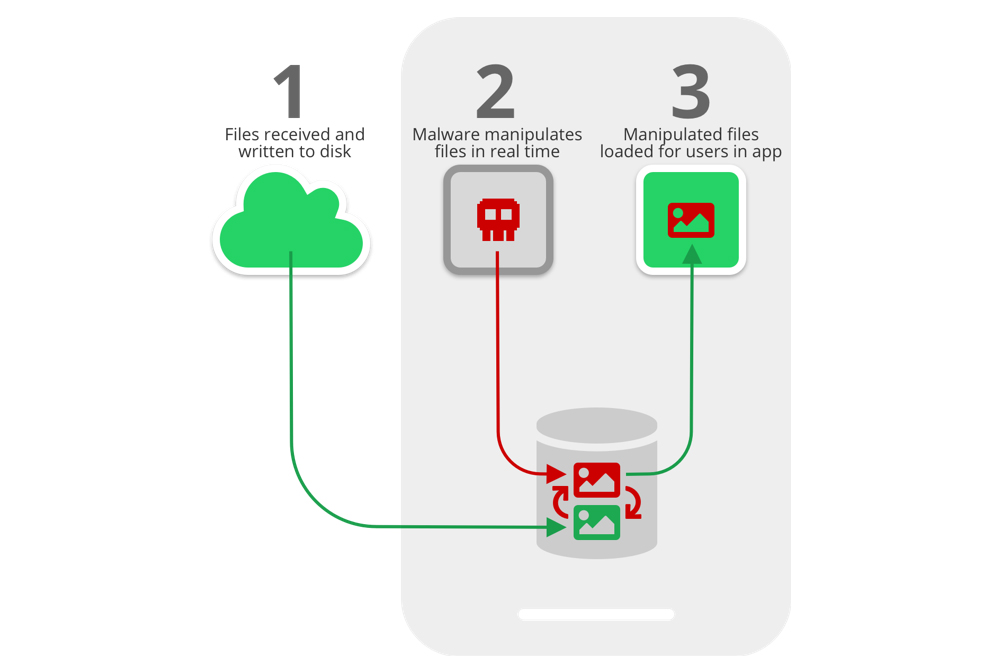
As shown in above image, in the time between when files are first received on a device and written to the disk (STEP 1), and when they are loaded for users to consume via the apps (STEP 3), malware can instantaneously analyse and manipulate the files (or just replace them with the attacker’s chosen files) for malicious gain (STEP 2).
The thumbnail that appears in the notification that users see will also show the manipulated image or file, so recipients will have no indication that files were changed. What’s terrifying is that the data can be manipulated on WhatsApp both when sending files (which means the attack is launched on the sender’s device) and when receiving files (that is, the attack is happening on the receiving device).
Potential usage scenarios include:
- Image manipulation: A seemingly innocent, but actually malicious, app downloaded by a user can manipulate personal photos in near-real time and without the victim knowing.
- Payment manipulation: A malicious actor could manipulate an invoice sent by a vendor to a customer, to trick the customer into making a payment to an illegitimate account.
- Audio message spoofing: Using voice reconstruction via deep learning technology, an attacker could alter an audio message for their own personal gain or to wreak havoc.
- Fake news: In Telegram, admins use the concept of “channels” to broadcast messages to an unlimited number of subscribers who consume the published content. An attacker could change the media files that appear in a trusted channel feed in real time to communicate falsities.
Even the Android developer documentation mentions the threat of saving files on external storage. “Internal storage is best when you want to be sure that neither the user nor other apps can access your files.” On the contrary, “external storage is the best place for files that don't require access restrictions and for files that you want to share with other apps or allow the user to access with a computer.”